HAIJA INTEL REPORT
Tweets / X
9 items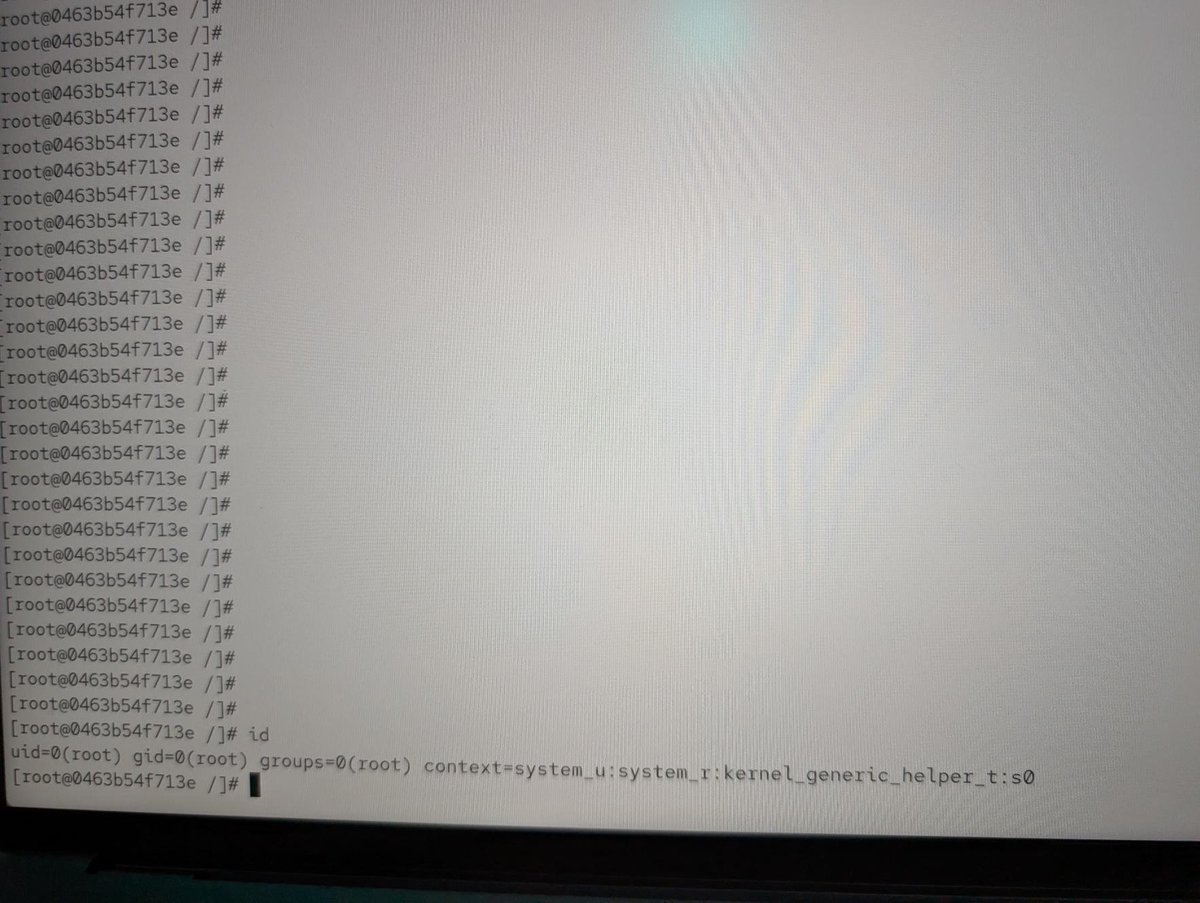





Regular sources
6 itemsMaximum Severity Cisco SD-WAN Bug Exploited in the Wild
This is the second time this year a threat actor has leveraged a CVSS 10.0 vulnerability in Cisco's network control system.
18-year-old NGINX vulnerability allows DoS, potential RCE
An 18-year-old flaw in the NGINX open-source web server, discovered using an autonomous scanning system, can be exploited for denial of service and, under certain condit…
When configuration becomes a vulnerability: Exploitable misconfigurations in AI apps
Exposed UIs, weak authentication, and risky defaults could turn cloud-native AI apps on Kubernetes into potential targets by threat actors. Learn how exploitable misconf…
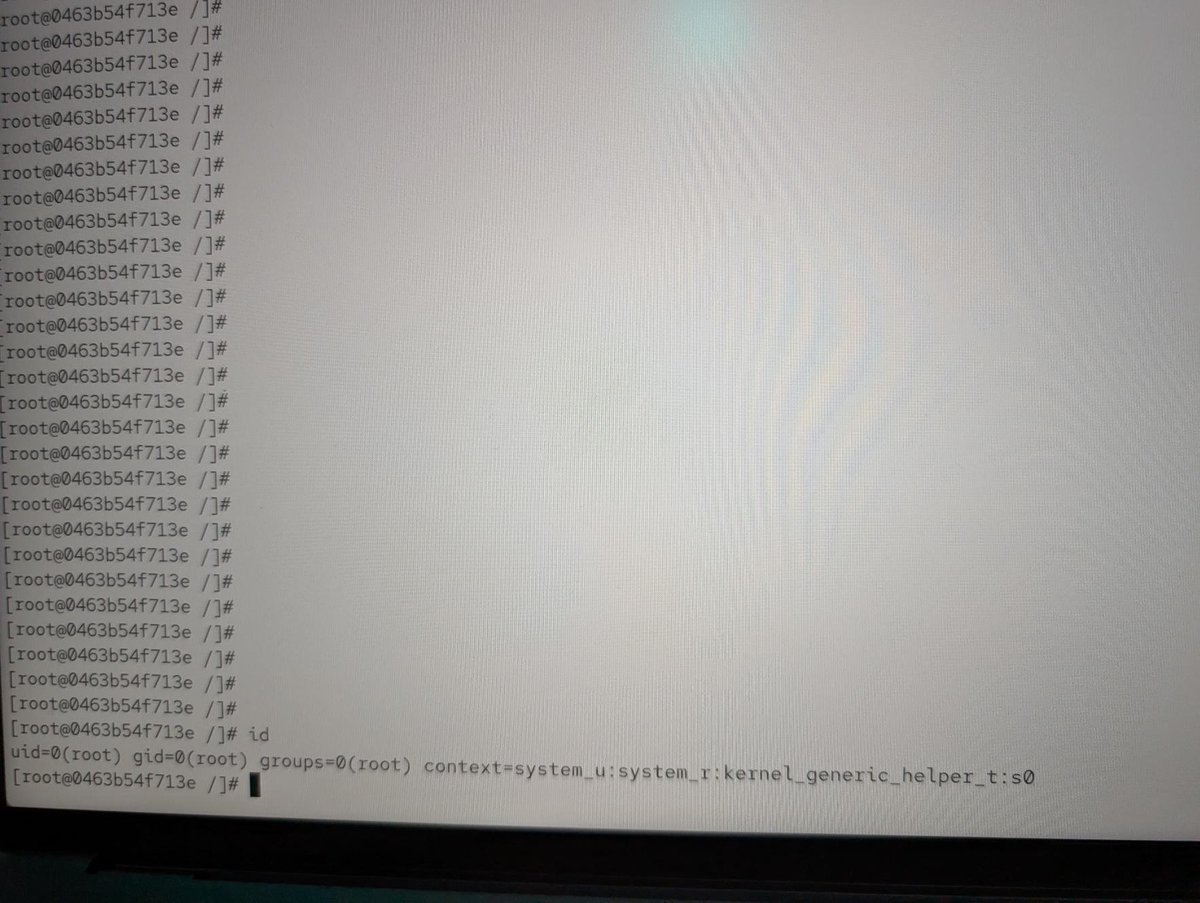
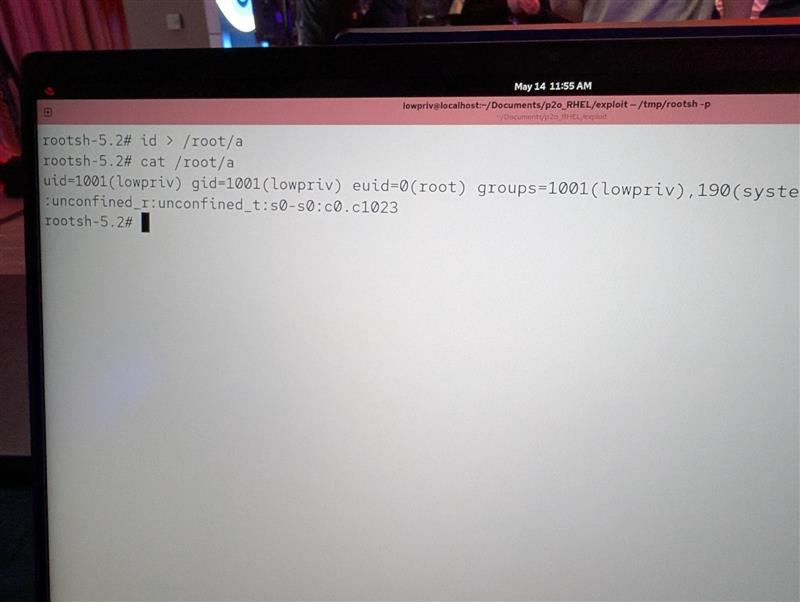
Re: Linux kernel LPE ("fragnesia", copyfail 3.0)
Posted by Jan Schaumann on May 13 Solar Designer wrote: https://github.com/v12-security/pocs/tree/main/fragnesia https://lists.openwall.net/netdev/2026/05/13/79, so Linu… | Posted by Salvatore Bonaccorso on May 14 Hi, https://lore.kernel.org/netdev/agVpIsaSherjHTYg@sultan-box/ for review https://lore.kernel.org/netdev/agW4vC0r8QOUKtRT@v4bel…
[vim-security] Vimscript Code Injection in netrw NetrwMarkFile() via crafted filename affects Vim < 9.2.480
Posted by Christian Brabandt on May 14 Vimscript Code Injection in netrw NetrwMarkFile() via crafted filename affects Vim < 9.2.480 =====================================…
Siemens gWAP
View CSAF Summary Siemens gPROMS Web Applications Publisher (gWAP) is affected by a remote code execution vulnerability introduced through a third-party component, namel…