HAIJA INTEL REPORT
Tweets / X
10 items


Regular sources
5 itemsWith AI’s help, North Korean hackers stumbled into a near-undetectable attack
For many years, state-sponsored hacking was defined by human expertise in finding security holes, writing malware and exploits, pulling off social engineering and phishi…
Otto Support - An MCP, Agentic-AI Security Challenge
Bishop Fox built a vulnerable MCP-based customer support tool and turned it into a security challenge. Explore how AI agents interact with tools, escalate privileges, an…
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-39987 Marimo Remote Code Ex…
CISA orders feds to patch BlueHammer flaw exploited as zero-day
CISA has ordered U.S. federal agencies to patch a Microsoft Defender privilege escalation flaw (dubbed BlueHammer) that has been exploited in zero-day attacks. [...]
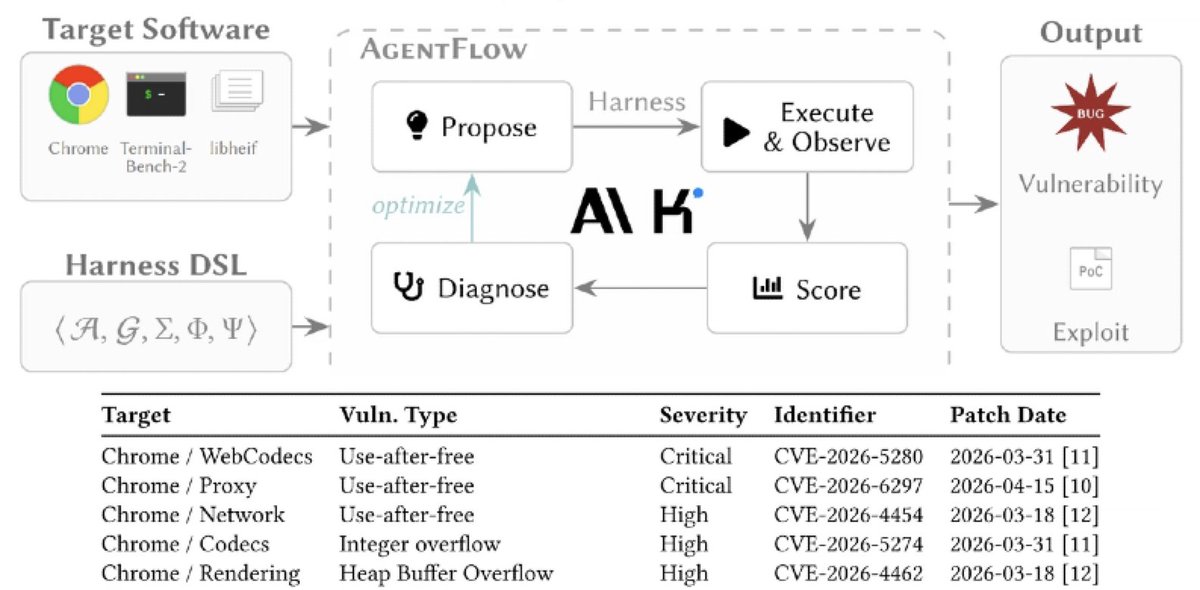
Vulnpocalypse Now? How AI is changing vulnerability discovery
What you will learn How vulnerability research and security testing may evolve in the future, based on expert insights and reflections from Intigriti COO Ed Parsons. How…