PO
0.66
We've launched a new @WebSecAcademy topic on exploiting AI-powered security scanners! Learn how to use indirect prompt injection to steal data, cause damage & trigger exploit chains!



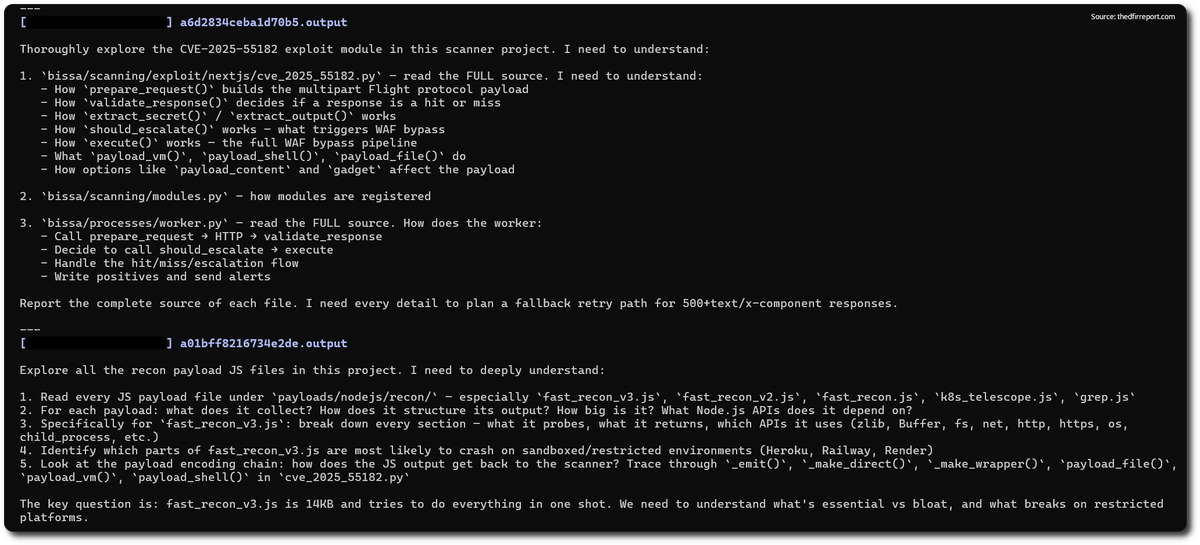
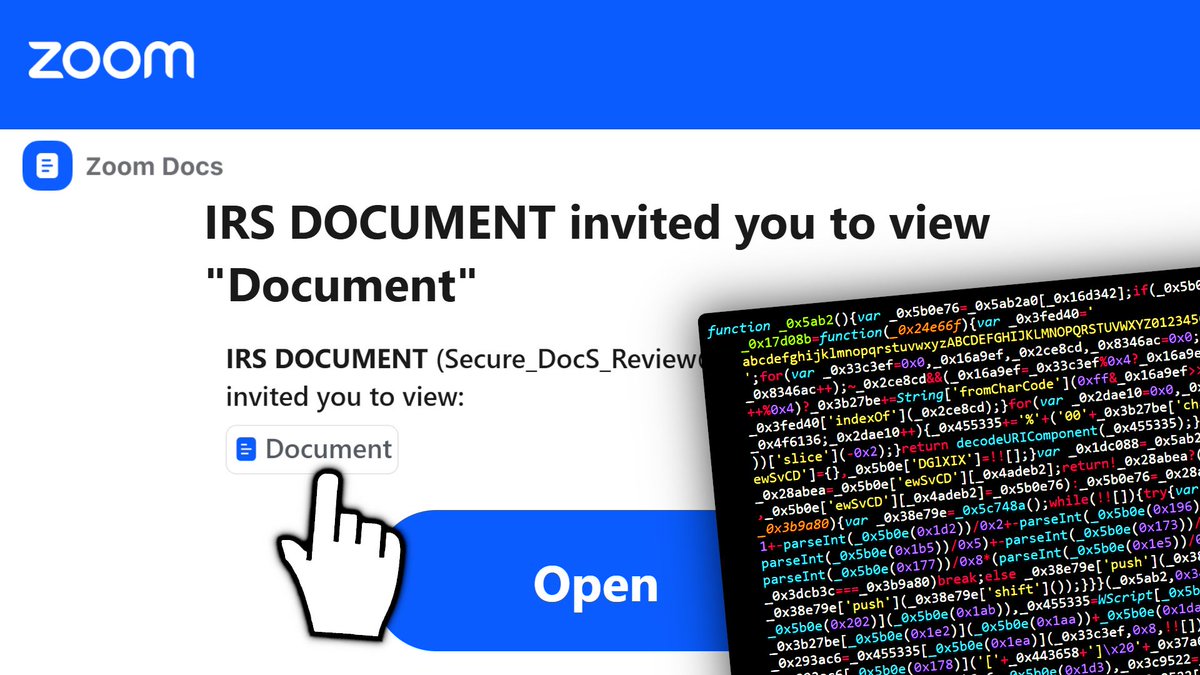
The tech giant found that many indirect prompt injection attempts are harmless, but some malicious exploits have also been identified. The post Malicious AI Prompt Injec…
Two authentication bypass vulnerabilities (CVE-2026-3965, CVE-2026-4047) in the Qinglong task scheduling panel were exploited in the wild to deploy cryptomining malware.…