











Cybersecurity researchers have discovered a critical "by design" weakness in the Model Context Protocol's (MCP) architecture that could pave the way for remote code exec…
Posted by Pico 🧬 on Apr 19 Hi, https://pypi.org/project/terminal-controller/) GitHub:...
Posted by Alan Coopersmith on Apr 18 https://blog.calif.io/p/we-asked-claude-to-audit-sagredos and https://github.com/califio/publications/tree/main/MADBugs/qmail https:…
Posted by Jarek Potiuk on Apr 17 Severity: low Affected versions: - Apache Airflow Keycloak Provider (apache-airflow-providers-keycloak) 0.0.1 before 0.7.0 Description: …
Authorities take down W3LL phishing ring, AgingFly malware steals Ukrainian government data, and actors exploit Nginx flaw to hijack servers.
Other noteworthy stories that might have slipped under the radar: ShinyHunters targets Rockstar Games, ShowDoc vulnerability exploited in the wild, and EPA to boost cybe…
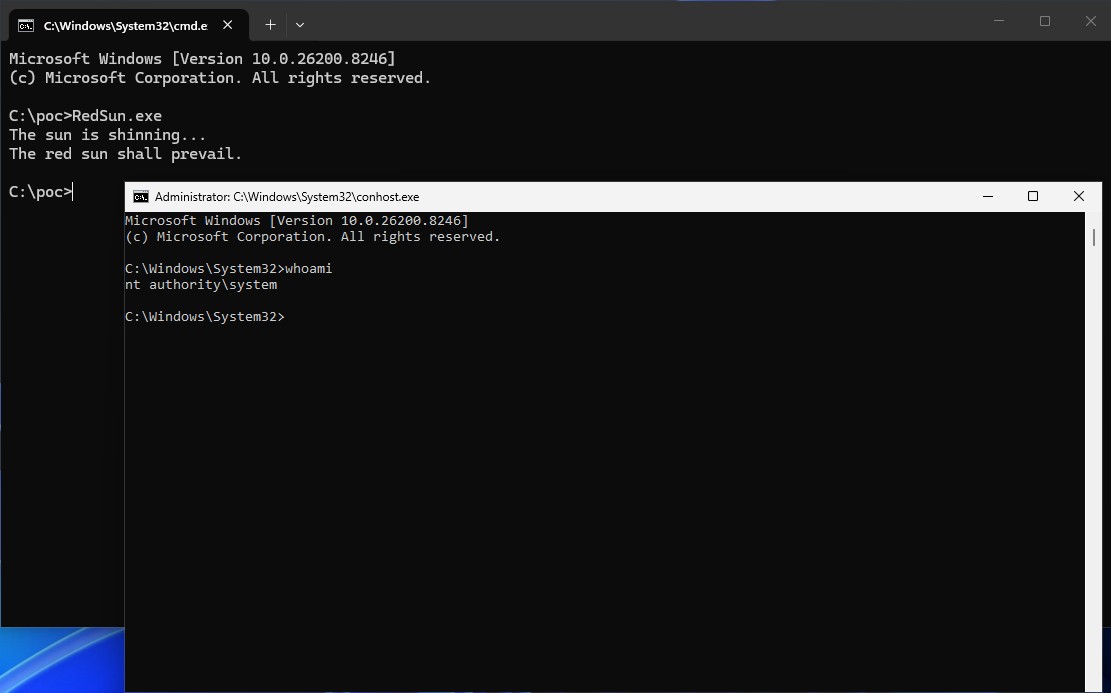
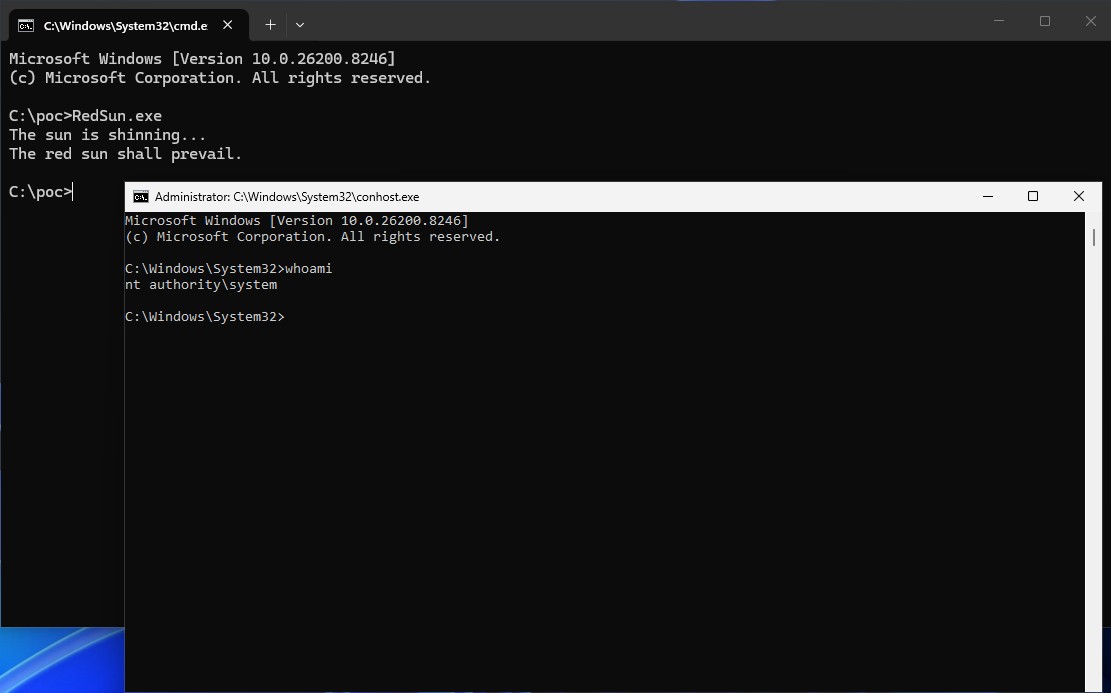
The security researcher who earlier this month published a proof-of-concept (PoC) exploit for a zero-day privilege escalation vulnerability in Microsoft Defender is back…
The remote code execution vulnerability tracked as CVE-2026-34197 came to light in early April. The post Recent Apache ActiveMQ Vulnerability Exploited in the Wild appea…
Posted by Matthias Ferdinand on Apr 19 [ hopefully, discussing binary releases is not off-topic ] Personally, I am guilty of not compiling packages myself (except for so…